The microCOMPLIANCE solution powered by HIPAA Secure Now! will provide you with the tools you need to comply with the HIPAA Security Rule. microCOMPLIANCE was developed by experts knowledgeable with the HIPAA Security Rule, computer and network security, and security training. The combination of these skills are apparent in the level of detail and knowledge that the service provides.
microCOMPLIANCE consists of the following:

18+ Policies and Procedures that address:
Administrative Safeguards
These provisions are defined in the Security Rule as the “administrative actions, policies, and procedures to manage the selection, development, implementation, and maintenance of security measures to protect electronic protected health information and to manage the conduct of the covered entity’s workforce in relation to the protection of that information.”
Physical Safeguards
These provisions are defined as the “physical measures, policies, and procedures to protect a covered entity’s electronic information systems and related buildings and equipment, from natural and environmental hazards, and unauthorized intrusion.”
Technical Safeguards
These provisions are defined as the “technology and the policy and procedures that protect electronic protected health information and control access to it (the EPHI).”
- Security Management Process
- Assigned Security Responsibility
- Workforce Security
- Information Access Management
- Security Awareness and Training
- Security Incident Procedure
- Contingency Planning
- Evaluation
- Business Associate Contracts
- Facility Access Controls
- Workstation Use
- Workstation Security
- Device and Media Control
- Access Control
- Audit Control
- Person or Entity Authentication
- Transmission Security
Each Policy and Procedure is a separate Microsoft Word document. The Policies and Procedures are customized with the name of your organization. Most of our clients do not require any changes or additional customizations to the Policies and Procedures but customization is an optional service if you need it.
In addition to the 18 Policies and Procedures, microCOMPLIANCE also includes forms and checklists that address:
- Device and Media Tracking
- Computer use guidelines
- Tracking access to server and equipment rooms
- Breach notification checklists

A detailed Risk Assessment is required under the HIPAA Security Rule. It is also considered the foundation of the HIPAA Security Rule.

The Security Management Process standard in the Security Rule requires organizations to “[i]mplement policies and procedures to prevent, detect, contain, and correct security violations.” (45 C.F.R. § 164.308(a)(1).) Risk analysis is one of four required implementation specifications that provide instructions to implement the Security Management Process standard. Section 164.308(a)(1)(ii)(A) states:
RISK ANALYSIS (Required).
Conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information (ePHI) held by the [organization].
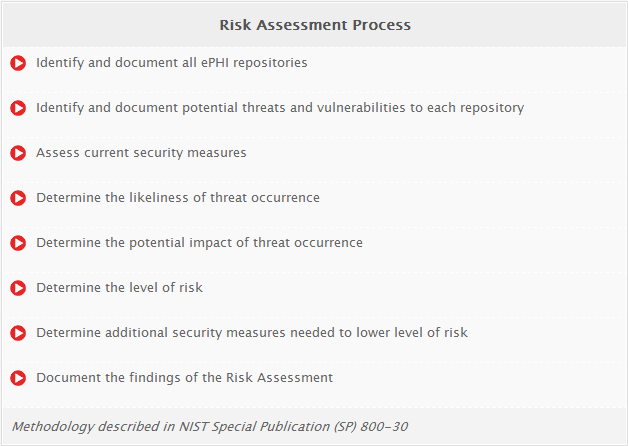
We will perform a detailed Risk Assessment that follows the methodology described in NIST Special Publication (SP) 800-30 Rev 1. Specifically the microCOMPLIANCE Risk Assessment will do the following:
The output of the Risk Assessment consists of a 10-15 page Executive Summary as well as a 20+ page detailed report. The Executive Summary is an easy to understand overview that discusses the current state of your overall risk to your systems that contain ePHI as well as recommendations to lower the risk to each system. The detailed report looks at each system that contains ePHI and documents the threats to the system, the vulnerabilities to the system, the current safeguards in place to protect the system and the additional recommended safeguards to lower the risk to the system.
The Risk Assessment report will give you a good understanding of the risks to ePHI and provide you with specific steps and actions that you should take to lower the risk.

HIPAA Security Training and Compliance Testing:
One of the most important steps you can take to protect ePHI and patient information is to provide security training to all of your employees. Security training is a requirement under the HIPAA Security Rule

STANDARD § 164.308(a)(5) Security awareness and training. Implement a security awareness and training program for all members of its workforce (including management). Security training for all new and existing members of the covered entity’s workforce is required by the compliance date of the Security Rule. In addition, periodic retraining should be given whenever environmental or operational changes affect the security of EPHI. Changes may include: new or updated policies and procedures; new or upgraded software or hardware; new security technology; or even changes in the Security Rule.-Department of Health and Human Services Security Standards: Administrative Safeguard
microCOMPLIANCE provides in-depth training on the HIPAA Security Rule as well as advice for best practices in protecting ePHI and patient information. The training is provided in an online format which is both engaging and convenient to your staff. Some of the topics covered in the training include:
Training Topics
- What is the HIPAA Security Rule?
- Understanding ePHI and PII
- Protecting ePHI
- Protecting Passwords
- Auditing ePHI
- Recognizing and Preventing Malware
- Using Encryption
- Security Breaches and Violations
- Practical Security Steps
- Many more topics
Training usually takes around 1 hour to complete. Your staff can start a training session, stop and resume the session from where they left off. They can take the training during work hours or complete the training at home after hours. Feedback from our clients regarding the training has been very positive.
Once your staff has completed the online training, they will take a short 15-20 question online quiz to demonstrate their knowledge regarding the HIPAA Security Rule. If they receive a score of 80% or higher, they will receive a certificate with their name that acknowledges that they have successfully completed the HIPAA Security Training. If they do not receive an 80% score on the quiz they can retake it as many times as they need to.
When your entire staff has completed training, you will receive a report that lists each of your staff members, the date they took the training and the highest score they received on the training quiz.

12 Months Use of the HIPAA Secure Compliance Portal
Included in the microCOMPLIANCE Service is 12 months access to the HIPAA Secure Compliance Portal. The HIPAA Secure Compliance Portal makes it easy to manage everything that you need to achieve and stay compliant with the HIPAA Security Rule.
microCOMPLIANCE HIPAA Secure Now! is comprehensive and affordable!

