Email and Spam Protection
Protect your business from online threats

Fast, efficient communication is one of the most important tools for running a successful business. While the benefits of email are undeniable, if you’re not adequately protected, you are leaving your business vulnerable to online attacks including spam, phishing, viruses and malware. With Email & Spam Protection from Micro Enterprises, your business can enjoy a reliable email system without being exposed to the safety threats associated with email.
Don't let online threats be the downfall of your business. Email & Spam Protection from Micro Enterprises assures your email is working to benefit your company, and not leaving you vulnerable to security problems.
By choosing Email & Spam Protection from Micro Enterprises you will:
- Improve email access – with flexible search options and attachment & message archiving
- Refine business processes – ease the pressure on your server by offloading huge amounts of storage
- Ensure the security of your email – prevent online threats and safeguard your business
- Simplify systems – get complete email indexing and easy access to your data
Overview
microDEFENDER Total Control (MTC) is a hosted email security service that blocks unwanted email before it reaches the corporate network. MicroDEFENDER’s unique technology also identifies address-sharing and the sources of spam, and provides concrete tools for preserving the integrity of one’s primary email address. Automatic inbound email queuing assures email continuity in the event of a local server outage, and outbound email filtering protects one’s reputation and helps to avoid the business disruption of IP address blacklisting. microDEFENDER’s service provides the configurability that IT Solution Providers need to address a wide range of customer requirements, with the automation and simplicity that ISPs require for their subscribers. Implementation simply requires an MX record change. The following diagram describes the various stages in MTC’s defense-indepth. With its bredth of capabilities, microDEFENDER’s defense is also uniquely configurable, providing the versatility that email administrators and solution providers require to address the widest range of end-user requirements. Mail for a specific user will only be subjected to the tests
dictated by their configuration. Additionally, the architecture is extensible, so that new defenses can be added as they become available or desirable.
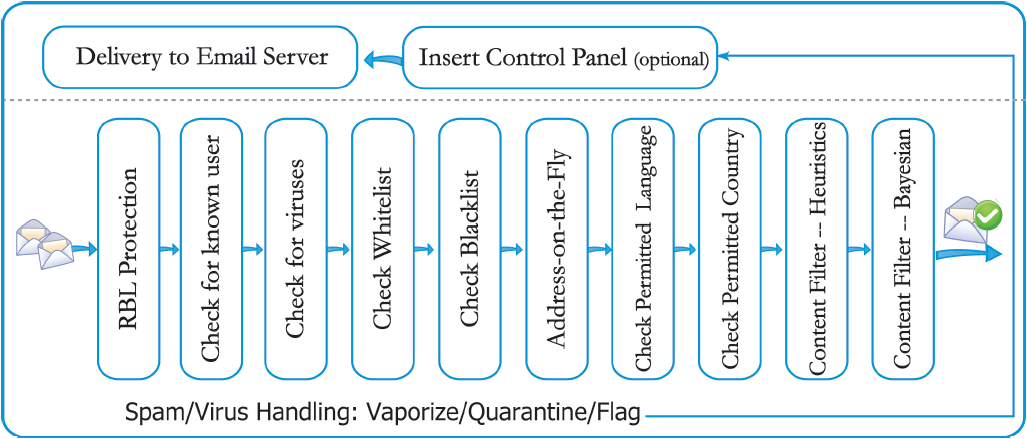
The first two layers of defense are designed to eliminate inbound emails destined for unknown users at your domain, so called Directory Harvesting Attacks. Currently, 80-90% of all messages traveling over the Internet are actually sent to unsers that don’t exist at the target domain.
microDEFENDER Permitted Countries
This capability further augments content filtering by blocking messages from any country other than those specifically approved for delivery at the enterprise and individual user levels. Delivery
Address-on-the-Fly™
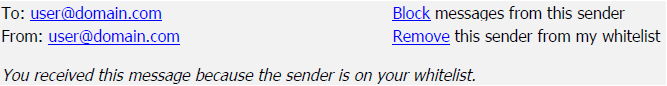
microDEFENDER makes it easy for users to employ alternate aliases for a single inbox. Address-on-the-Fly enables users to spontaneously disclose a purpose-specific address on a Web site, in a discussion forum, in print or conversation, etc., without having to manually configure that address ahead of time. These addresses take the form of a root name plus a suffix of the user’s own choosing. For example, to register on eBay, Jane Doe might disclose the address jdoe.ebay@herdomain.com, where the “.ebay” suffix serves as an “email PIN” that assures delivery of email sent to this address. Addresses are independently controllable by policy through simple interaction with the Total Control Panel, so that legitimate users of the address can be “locked down” in the event the address is ever harvested and abused by a spammer.
microDEFENDER Outbound Mail Auditing (MOMA)
microDEFENDER blocks outbound email that contains spam and viruses. It also identifies and prevents open relay conditions and potential compromised, “zombie” PCs, in order to prevent our customers from inadvertently spamming their contacts and to avoid IP address blacklisting, with the business disruption that accompanies that unpleasant outcome.
Avoid the threat of online attacks.



